IAT/IAM Certification Quiz
Skills Check Summary
0 of 90 Questions completed
Questions:
Information
You have already completed the skills check before. Hence you can not start it again.
Skills Check is loading…
You must sign in or sign up to start the skills check.
You must first complete the following:
Results
Results
0 of 90 Questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 point(s), (0)
Earned Point(s): 0 of 0, (0)
0 Essay(s) Pending (Possible Point(s): 0)
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- Current
- Review
- Answered
- Correct
- Incorrect
-
Question 1 of 90
1. Question
Multiple organizations operating in the same vertical want to provide seamless wireless access for their employees as they visit the other organizations. Which of the following should be implemented if all the organizations use the native 802.1x client on their mobile devices?
CorrectIncorrect -
Question 2 of 90
2. Question
Which of the following attacks specifically impact data availability?
CorrectIncorrect -
Question 3 of 90
3. Question
A security analyst is hardening a server with the directory services role installed. The analyst must ensure LDAP traffic cannot be monitored or sniffed and maintains compatibility with LDAP clients. Which of the following should the analyst implement to meet these requirements? (Choose two.)
CorrectIncorrect -
Question 4 of 90
4. Question
Which of the following characteristics differentiate a rainbow table attack from a brute force attack? (Choose two.)
CorrectIncorrect -
Question 5 of 90
5. Question
Which of the following threat actors is MOST likely to steal a company’s proprietary information to gain a market edge and reduce time to market?
CorrectIncorrect -
Question 6 of 90
6. Question
A penetration tester is crawling a target website that is available to the public. Which of the following represents the actions the penetration tester is performing?
CorrectIncorrect -
Question 7 of 90
7. Question
Which of the following best describes routine in which semicolons, dashes, quotes, and commas are removed from a string?
CorrectIncorrect -
Question 8 of 90
8. Question
Which of the following explains why vendors publish MD5 values when they provide software patches for their customers to download over the Internet?
CorrectIncorrect -
Question 9 of 90
9. Question
An organization has determined it can tolerate a maximum of three hours of downtime. Which of the following has been specified?
CorrectIncorrect -
Question 10 of 90
10. Question
Which of the following types of keys is found in a key escrow?
CorrectIncorrect -
Question 11 of 90
11. Question
Despite having implemented password policies, users continue to set the same weak passwords and reuse old passwords. Which of the following technical controls would help prevent these policy violations? (Choose two)
CorrectIncorrect -
Question 12 of 90
12. Question
Which of the following types of cloud infrastructures would allow several organizations with similar structures and interests to realize the benefits of shared storage and resources?
CorrectIncorrect -
Question 13 of 90
13. Question
A company determines that it is prohibitively expensive to become compliant with new credit card regulations. Instead, the company decides to purchase insurance to cover the cost of any potential loss. Which of the following is the company doing?
CorrectIncorrect -
Question 14 of 90
14. Question
Malicious traffic from an internal network has been detected on an unauthorized port on an application server. Which of the following network-based security controls should the engineer consider implementing?
CorrectIncorrect -
Question 15 of 90
15. Question
A network administrator wants to implement a method of securing internal routing. Which of the following should the administrator implement?
CorrectIncorrect -
Question 16 of 90
16. Question
Which of the following encryption methods does PKI typically use to securely protect keys?
CorrectIncorrect -
Question 17 of 90
17. Question
A department head at a university resigned on the first day of the spring semester. It was subsequently determined that the department head deleted numerous files and directories from the server-based home directory while the campus was closed. Which of the following policies or procedures could have prevented this from occurring?
CorrectIncorrect -
Question 18 of 90
18. Question
An organization finds that most help desk calls are regarding account lockout due to a variety of applications running on different systems. Management is looking for a solution to reduce the number of account lockouts while improving security.
Which of the following is the BEST solution for this organization?
CorrectIncorrect -
Question 19 of 90
19. Question
Ann, a security administrator, has been instructed to perform fuzz-based testing on the company’s applications. Which of the following best describes what she will do?
CorrectIncorrect -
Question 20 of 90
20. Question
A network administrator at a small office wants to simplify the configuration of mobile clients connecting to an encrypted wireless network. Which of the following should be implemented if the administrator does not want to provide the wireless password or the certificate to the employees?
CorrectIncorrect -
Question 21 of 90
21. Question
When connected to a secure WAP, which of the following encryption technologies is MOST likely to be configured when connecting to WPA2–PSK?
CorrectIncorrect -
Question 22 of 90
22. Question
When configuring settings in a mandatory access control environment, which of the following specifies the subjects that can access specific data objects?
CorrectIncorrect -
Question 23 of 90
23. Question
A high–security defense installation recently begun utilizing large guard dogs that bark very loudly and excitedly at the slightest provocation. Which of the following types of controls does this BEST describe?
CorrectIncorrect -
Question 24 of 90
24. Question
A company’s user lockout policy is enabled after five unsuccessful login attempts. The help desk notices a user is repeatedly locked out over the course of a workweek. Upon contacting the user, the help desk discovers the user is on vacation and does not have network access.
Which of the following types of attacks are MOST likely occurring? (Select two.)
CorrectIncorrect -
Question 25 of 90
25. Question
Ann. An employee in the payroll department, has contacted the help desk citing multiple issues with her device, including Slow performance Word documents, PDFs, and images no longer opening a pop-up. Ann states the issues began after she opened an invoice that a vendor emailed to her. Upon opening the invoice, she had to click several security warnings to view it in her word processor. With which of the following is the device MOST likely infected?
CorrectIncorrect -
Question 26 of 90
26. Question
A company is terminating an employee for misbehavior. Which of the following steps is MOST important in the process of disengagement from this employee?
CorrectIncorrect -
Question 27 of 90
27. Question
A company is developing a new secure technology and requires computers being used for development to be isolated. Which of the following should be implemented to provide the MOST secure environment?
CorrectIncorrect -
Question 28 of 90
28. Question
A user clicked an email link that led to a website than infected the workstation with a virus. The virus encrypted all the network shares to which the user had access. The virus was not deleted or blocked by the company’s email filter, website filter, or antivirus. Which of the following describes what occurred?
CorrectIncorrect -
Question 29 of 90
29. Question
An organization wishes to provide better security for its name resolution services. Which of the following technologies BEST supports the deployment of DNSSEC at the organization?
CorrectIncorrect -
Question 30 of 90
30. Question
A company hires a consulting firm to crawl its Active Directory network with a non-domain account looking for unpatched systems. Actively taking control of systems is out of scope, as is the creation of new administrator accounts. For which of the following is the company hiring the consulting firm?
CorrectIncorrect -
Question 31 of 90
31. Question
An administrator is replacing a wireless router. The configuration of the old wireless router was not documented before it stopped functioning. The equipment connecting to the wireless network uses older legacy equipment that was manufactured prior to the release of the 802.11i standard. Which of the following configuration options should the administrator select for the new wireless router?
CorrectIncorrect -
Question 32 of 90
32. Question
An application team is performing a load-balancing test for a critical application during off-hours and has requested access to the load balancer to review which servers are up without having the administrator on call. The security analyst is hesitant to give the application team full access due to other critical applications running on the load balancer.
Which of the following is the BEST solution for security analyst to process the request?
CorrectIncorrect -
Question 33 of 90
33. Question
A security analyst is hardening an authentication server. One of the primary requirements is to ensure there is mutual authentication and delegation. Given these requirements, which of the following technologies should the analyst recommend and configure?
CorrectIncorrect -
Question 34 of 90
34. Question
Two users need to send each other emails over unsecured channels. The system should support the principle of non-repudiation. Which of the following should be used to sign the user’s certificates?
CorrectIncorrect -
Question 35 of 90
35. Question
Which of the following attack types BEST describes a client–side attack that is used to manipulate an HTML iframe with JavaScript code via a web browser?
CorrectIncorrect -
Question 36 of 90
36. Question
An incident responder receives a call from a user who reports a computer is exhibiting symptoms consistent with a malware infection. Which of the following steps should the responder perform NEXT?
CorrectIncorrect -
Question 37 of 90
37. Question
A senior incident response manager receives a call about an external IP communicating with internal computers during off hours. Which of the following types of malware is MOST likely causing this issue?
CorrectIncorrect -
Question 38 of 90
38. Question
Which of the following technologies employ the use of SAML? (Choose two.)
CorrectIncorrect -
Question 39 of 90
39. Question
Which of the following network vulnerability scan indicators BEST validates a successful, active scan?
CorrectIncorrect -
Question 40 of 90
40. Question
Which of the following is the BEST explanation of why control diversity is important in a defense–in–depth architecture?
CorrectIncorrect -
Question 41 of 90
41. Question
An information security specialist is reviewing the following output from a Linux server.
user@server:~$ crontab -l
5**** /usr/local/bin/backup.sh
#!/bin/bash
if ! grep – – quiet joeuser/etc/passwd
then rm -rf /
fi
Based on the above information, which of the following types of malware was installed on the server?
CorrectIncorrect -
Question 42 of 90
42. Question
In terms of encrypting data, which of the following is BEST described as a way to safeguard password data by adding random data to it in storage?
CorrectIncorrect -
Question 43 of 90
43. Question
A system administrator wants to provide for and enforce wireless access accountability during events where external speakers are invited to make presentations to a mixed audience of employees and non-employees. Which of the following should the administrator implement?
CorrectIncorrect -
Question 44 of 90
44. Question
Which of the following would MOST likely appear in an uncredentialed vulnerability scan?
CorrectIncorrect -
Question 45 of 90
45. Question
A security analyst observes the following events in the logs of an employee workstation
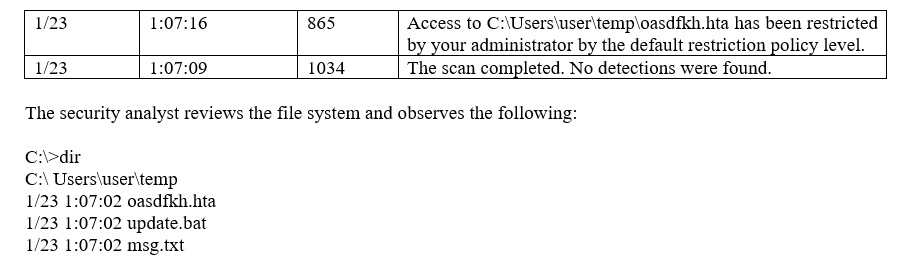
Given the information provided, which of the following MOST likely occurred on the workstation?
CorrectIncorrect -
Question 46 of 90
46. Question
When considering a third–party cloud service provider, which of the following criteria would be the BEST to include in the security assessment process? (Choose two.)
CorrectIncorrect -
Question 47 of 90
47. Question
Which of the following occurs when the security of a web application relies on JavaScript for input validation?
CorrectIncorrect -
Question 48 of 90
48. Question
An organization’s file server has been virtualized to reduce costs. Which of the following types of backups would be MOST appropriate for the particular file server?
CorrectIncorrect -
Question 49 of 90
49. Question
An employer requires that employees use a key-generating app on their smartphones to log into corporate applications. In terms of authentication of an individual, this type of access policy is BEST defined as
CorrectIncorrect -
Question 50 of 90
50. Question
A manager wants to distribute a report to several other managers within the company. Some of them reside in remote locations that are not connected to the domain but have a local server. Because there is sensitive data within the reportand the size of the report is beyond the limit of the email attachment size, emailing the report is not an option.
Which of the following protocols should be implemented to distribute the report securely? (Choose three.)
CorrectIncorrect -
Question 51 of 90
51. Question
Which of the following must be intact for evidence to be admissible in court?
CorrectIncorrect -
Question 52 of 90
52. Question
Which of the following cryptography algorithms will produce a fixed-length, irreversible output?
CorrectIncorrect -
Question 53 of 90
53. Question
A technician suspects that a system has been compromised. The technician reviews the following log entry
WARNING– hash mismatch: C:\Window\SysWOW64\user32.dll
WARNING– hash mismatch: C:\Window\SysWOW64\kernel32.dllBased solely on the above information, which of the following types of malware is MOST likely installed on the system?
CorrectIncorrect -
Question 54 of 90
54. Question
Which of the following are the MAIN reasons why a systems administrator would install security patches in a staging environment before the patches are applied to the production server? (Choose two.)
CorrectIncorrect -
Question 55 of 90
55. Question
A Chief Information Officer (CIO) drafts an agreement between the organization and its employees. The agreement outlines ramifications for releasing information without consent and/or approvals. Which of the following BEST describes this type of agreement?
CorrectIncorrect -
Question 56 of 90
56. Question
Which of the following would meet the requirements for multifactor authentication?
CorrectIncorrect -
Question 57 of 90
57. Question
A manager suspects that an IT employee with elevated database access may be knowingly modifying financial transactions for the benefit of a competitor.
Which of the following practices should the manager implement to validate the concern?
CorrectIncorrect -
Question 58 of 90
58. Question
A penetration tester finds that a company’s login credentials for the email client were being sent in clear text.
Which of the following should be done to provide encrypted logins to the email server?
CorrectIncorrect -
Question 59 of 90
59. Question
Before an infection was detected, several of the infected devices attempted to access a URL that was similar to the company name but with two letters transposed. Which of the following BEST describes the attack vector used to infect the devices?
CorrectIncorrect -
Question 60 of 90
60. Question
Joe, a security administrator, needs to extend the organization’s remote access functionality to be used by staff while traveling. Joe needs to maintain separate access control functionalities for internal, external, and VOIP services.
Which of the following represents the BEST access technology for Joe to use?
CorrectIncorrect -
Question 61 of 90
61. Question
The availability of a system has been labeled as the highest priority.
Which of the following should be focused on the MOST to ensure the objective?
CorrectIncorrect -
Question 62 of 90
62. Question
Someone purchased several used hard drives from a company and was able to obtain confidential data from one of the hard drives. The company then discovers its information is posted online. Which of the following methods would have MOST likely prevented the data from being exposed while still keeping the drive usable?
CorrectIncorrect -
Question 63 of 90
63. Question
Which of the following are methods to implement HA in a web application server environment? (Choose two.)
CorrectIncorrect -
Question 64 of 90
64. Question
Which of the following precautions MINIMIZES the risk from network attacks directed at multi-function printers, as well as the impact on functionality at the same time?
CorrectIncorrect -
Question 65 of 90
65. Question
A company was recently audited by a third party. The audit revealed the company’s network devices were transferring files in the clear. Which of the following protocols should the company use to transfer files?
CorrectIncorrect -
Question 66 of 90
66. Question
During a monthly vulnerability scan, a server was flagged for being vulnerable to an Apache Struts exploit. Upon further investigation, the developer responsible for the server informs the security team that Apache Struts is not installed on the server.
Which of the following BEST describes how the security team should reach to this incident?
CorrectIncorrect -
Question 67 of 90
67. Question
A security engineer is configuring a wireless network that must support mutual authentication of the wireless client and the authentication server before users provide credentials. The wireless network must also support authentication with usernames and passwords.
Which of the following authentication protocols MUST the security engineer select?
CorrectIncorrect -
Question 68 of 90
68. Question
Which of the following vulnerability types would the type of hacker known as a script kiddie be MOST dangerous against?
CorrectIncorrect -
Question 69 of 90
69. Question
Which of the following cryptographic algorithms is irreversible?
CorrectIncorrect -
Question 70 of 90
70. Question
A security analyst receives an alert from a WAF with the following payload
var data= “<test test test>” ++
<../../../../../../etc/passwd>”Which of the following types of attacks is this?
CorrectIncorrect -
Question 71 of 90
71. Question
An organization is comparing and contrasting migration from its standard desktop configuration to the newest version of the platform. Before this can happen, the Chief Information Security Officer (CISO) voices the need to evaluate the functionality of the newer desktop platform to ensure interoperability with existing software in use by the organization. In which of the following principles of architecture and design is the CISO engaging?
CorrectIncorrect -
Question 72 of 90
72. Question
A network technician is setting up a segmented network that will utilize a separate ISP to provide wireless access to the public area for a company.
Which of the following wireless security methods should the technician implement to provide basic accountability for access to the public network?
CorrectIncorrect -
Question 73 of 90
73. Question
After a routine audit, a company discovers that engineering documents have been leaving the network on a particular port. The company must allow outbound traffic on this port, as it has a legitimate business use. Blocking the port would cause an outage.
Which of the following technology controls should the company implement?
CorrectIncorrect -
Question 74 of 90
74. Question
A security analyst reviews the following output
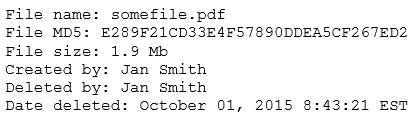
The analyst loads the hash into the SIEM to discover if this hash is seen in other parts of the network. After inspecting a large number of files, the security analyst reports the following
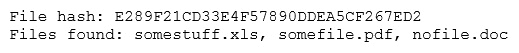
Which of the following is the MOST likely cause of the hash being found in other areas?
CorrectIncorrect -
Question 75 of 90
75. Question
Which of the following tools can aggregate intelligence from internal and external sources to provide fusion analysis and other insights, combine data and also provide for case management and automated workflow?
CorrectIncorrect -
Question 76 of 90
76. Question
In the context of cybersecurity, what does CIA stand for?
CorrectIncorrect -
Question 77 of 90
77. Question
In the context of cybersecurity, what does ICS stand for?
CorrectIncorrect -
Question 78 of 90
78. Question
OCSP is one of two common methods for maintaining the security of a server and other network resources by verifying the status of certificates. The other, older method, is known as Certificate Revocation List.
CorrectIncorrect -
Question 79 of 90
79. Question
A type of substitution cipher in which each letter in the plaintext is replaced by a letter some fixed number of positions down the alphabet
CorrectIncorrect -
Question 80 of 90
80. Question
What is the name of the Microsoft authentication protocol that was introduced with the release of Windows Server 2000, that is the only authentication protocol that uses tickets.
CorrectIncorrect -
Question 81 of 90
81. Question
PGP stands for Pretty Good Privacy
CorrectIncorrect -
Question 82 of 90
82. Question
Fences, guard dogs, lights, cameras and badges are examples of what type of security controls?
CorrectIncorrect -
Question 83 of 90
83. Question
You are developing a new web application for your company. Your boss is worried about the security of your application, mainly cross-site scripting and SQL injection. Which of the following would best defend against these attacks?
CorrectIncorrect -
Question 84 of 90
84. Question
The following attack is when an attacker sends falsified ARP messages over a network to link an attacker’s MAC address with the IP address of a legitimate computer or server on the network.
CorrectIncorrect -
Question 85 of 90
85. Question
Your boss calls you from the airport and is alarmed. He says there is an issue with your company web site and that it looks like it’s been hacked. You check it from your computer and it appears fine.
Which of the following is a reason that your boss is seeing a different page when visiting the companies website?
CorrectIncorrect -
Question 86 of 90
86. Question
Which of the following is a process regarding the detection of insider threats, targeted attacks, and financial fraud that tracks users, looks at patterns of human behavior, and then analyzes them to detect anomalies that may indicate potential threats.
CorrectIncorrect -
Question 87 of 90
87. Question
Which of the following is a domain-specific language designed for managing data, or for stream processing in relational data stream management systems (RDSMS).
CorrectIncorrect -
Question 88 of 90
88. Question
Which of the following is a secure, isolated private cloud hosted within a public cloud where customers can run code, store data, host websites, but the private cloud is hosted remotely by a public cloud service provider.
CorrectIncorrect -
Question 89 of 90
89. Question
Which cloud service model would a web developer most likely choose if their intentions were to create a web application?CorrectIncorrect -
Question 90 of 90
90. Question
Which of the following refers to the inability to deny responsibility for performing a specific action, such as creating information, sending a message, approving information, or receiving a message.
CorrectIncorrect

